Whois XML API is an application for Splunk. It allows conducting WHOIS search for domain names or IP addresses from within Splunk.
Prerequisites
You need to have Splunk Enterprise installed and configured. To do so, please refer to the official documentation.
Configuring the extension
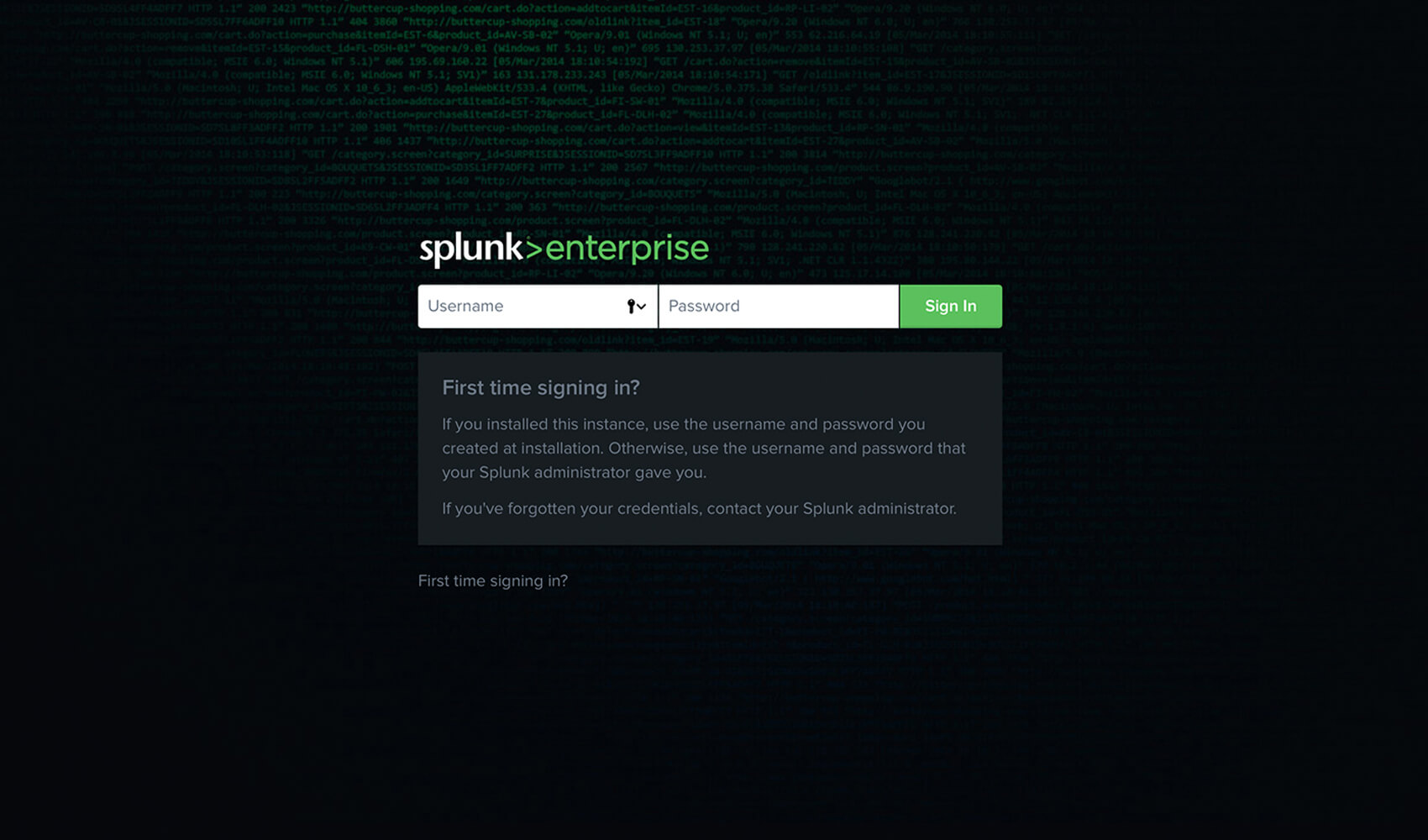
1. Log in to Splunk.
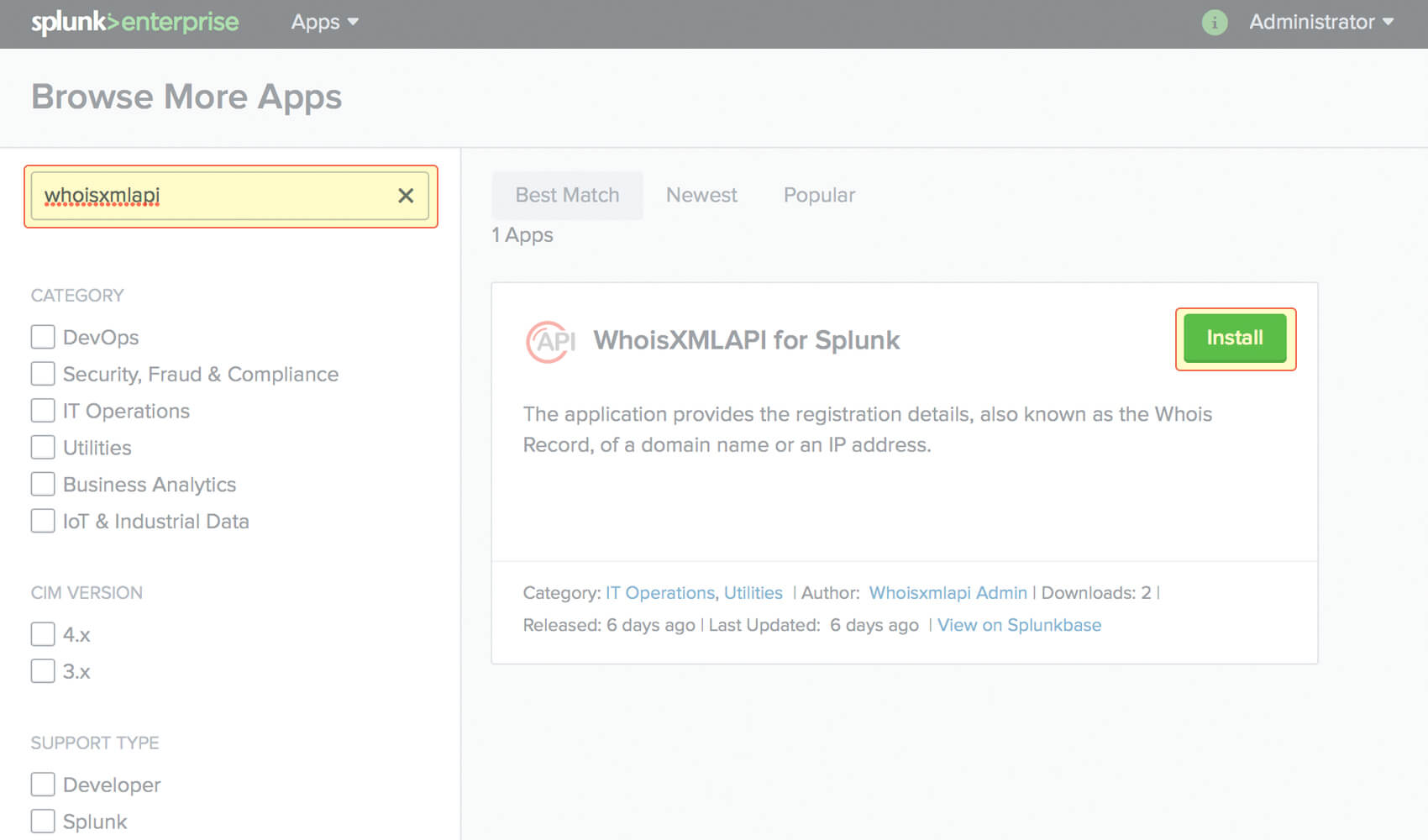
2. Download and install the application. This can be done from within Splunk. (https://splunkbase.splunk.com/app/4404)
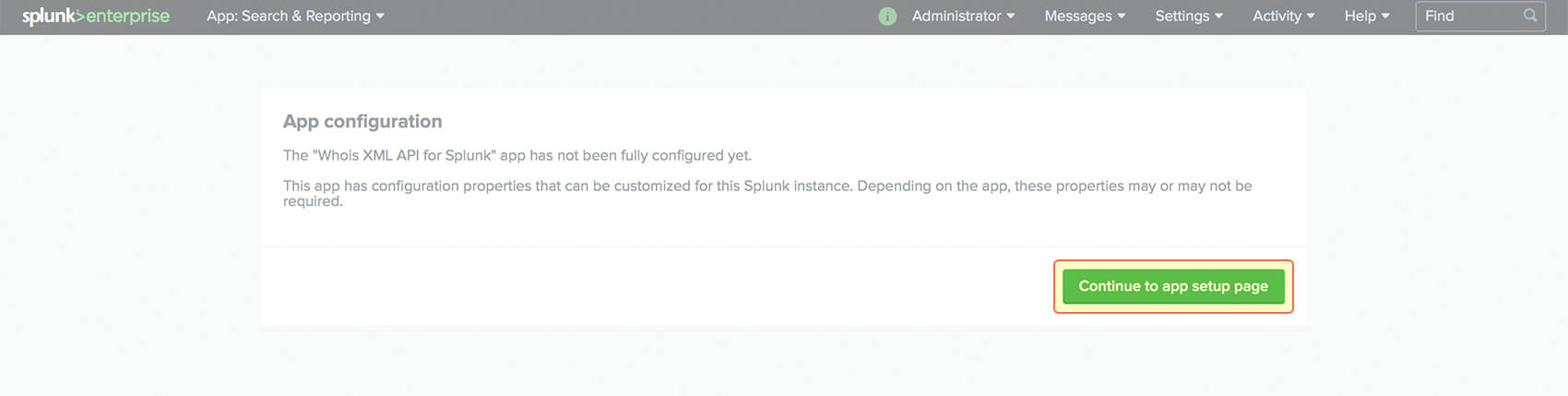
3. You can start configuring immediately once the application is installed.
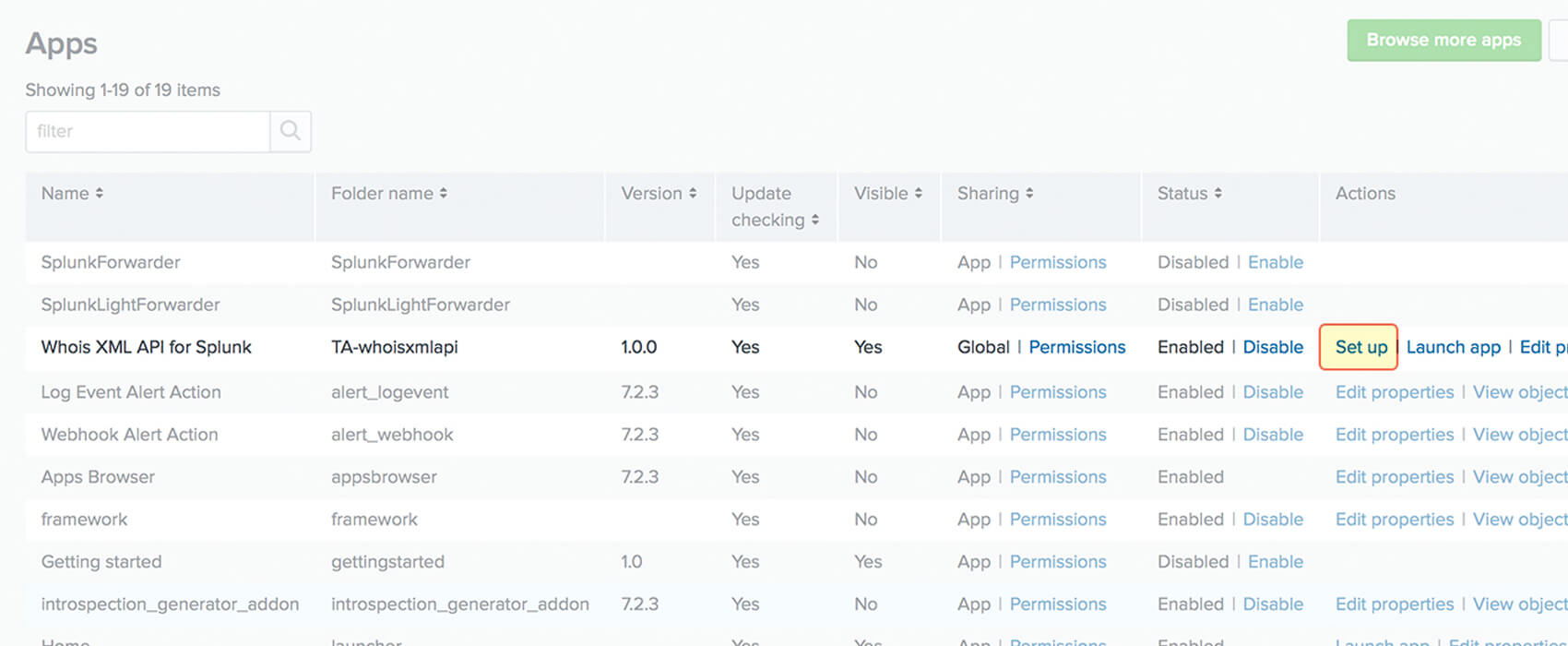
3.1 You can also configure the application on the Apps page. Click on Set up next to the application name.
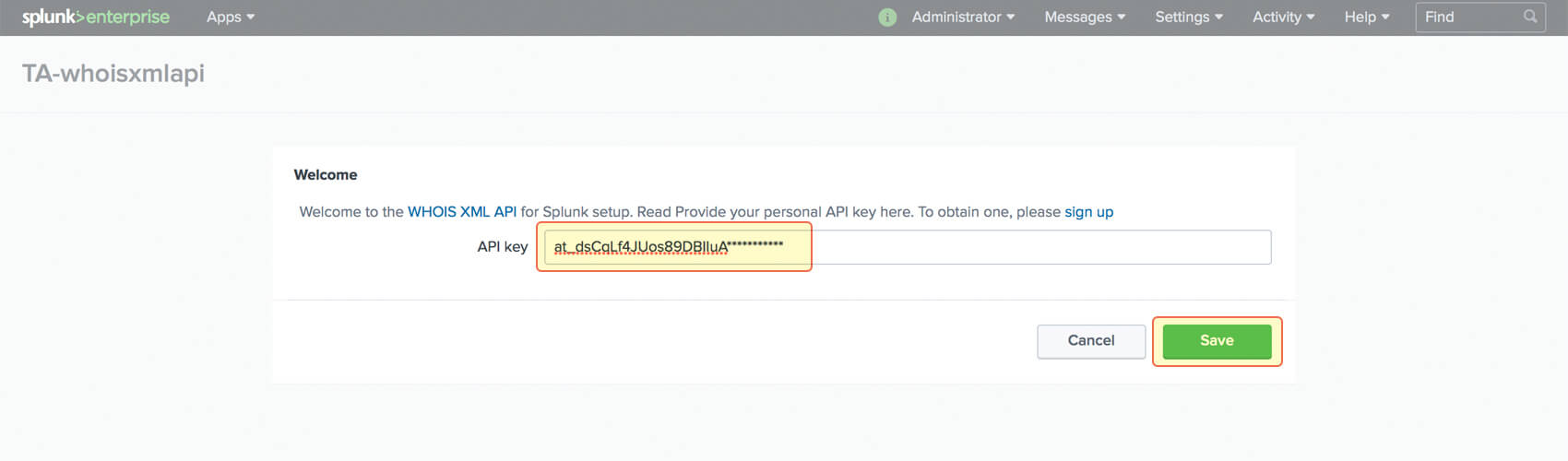
4. Fill in your API key and click on Save.
Using the extension
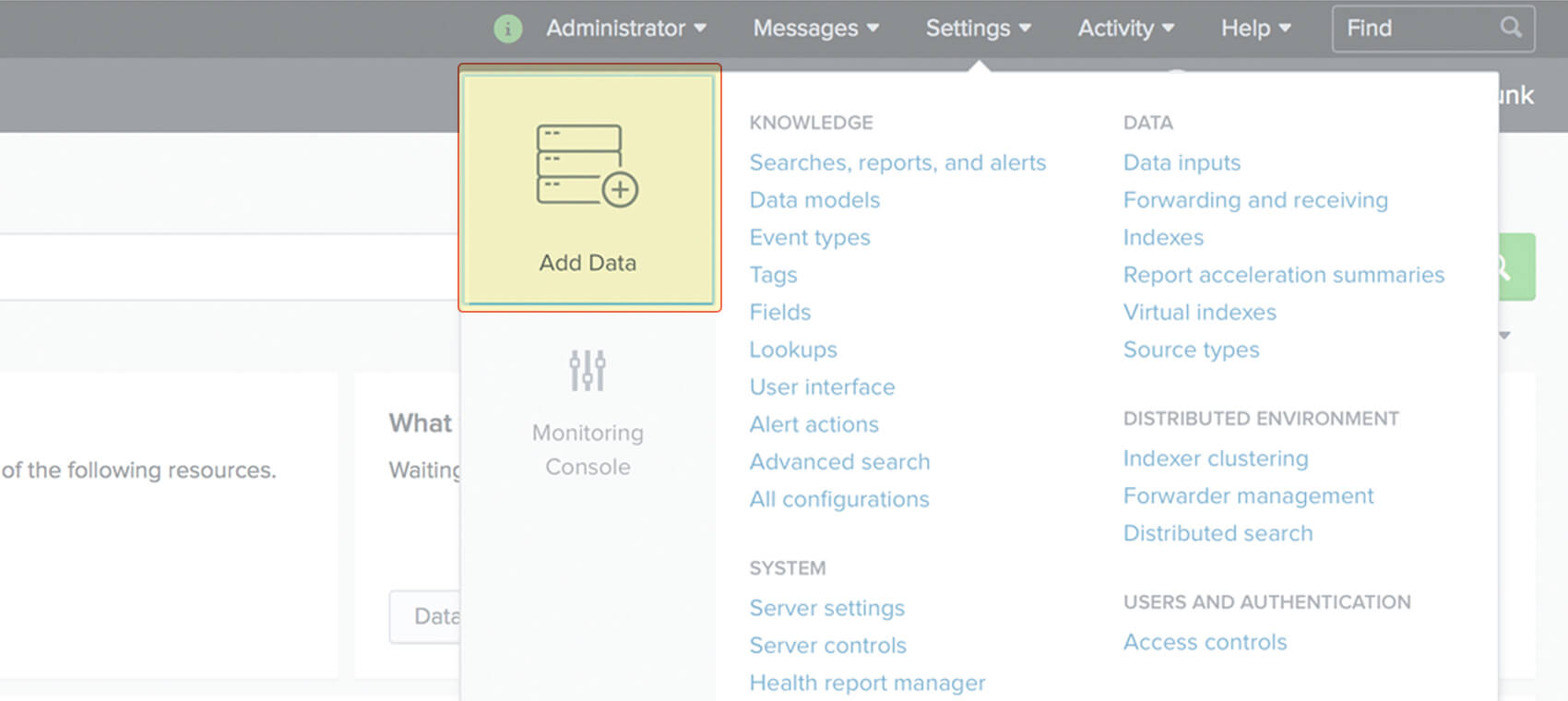
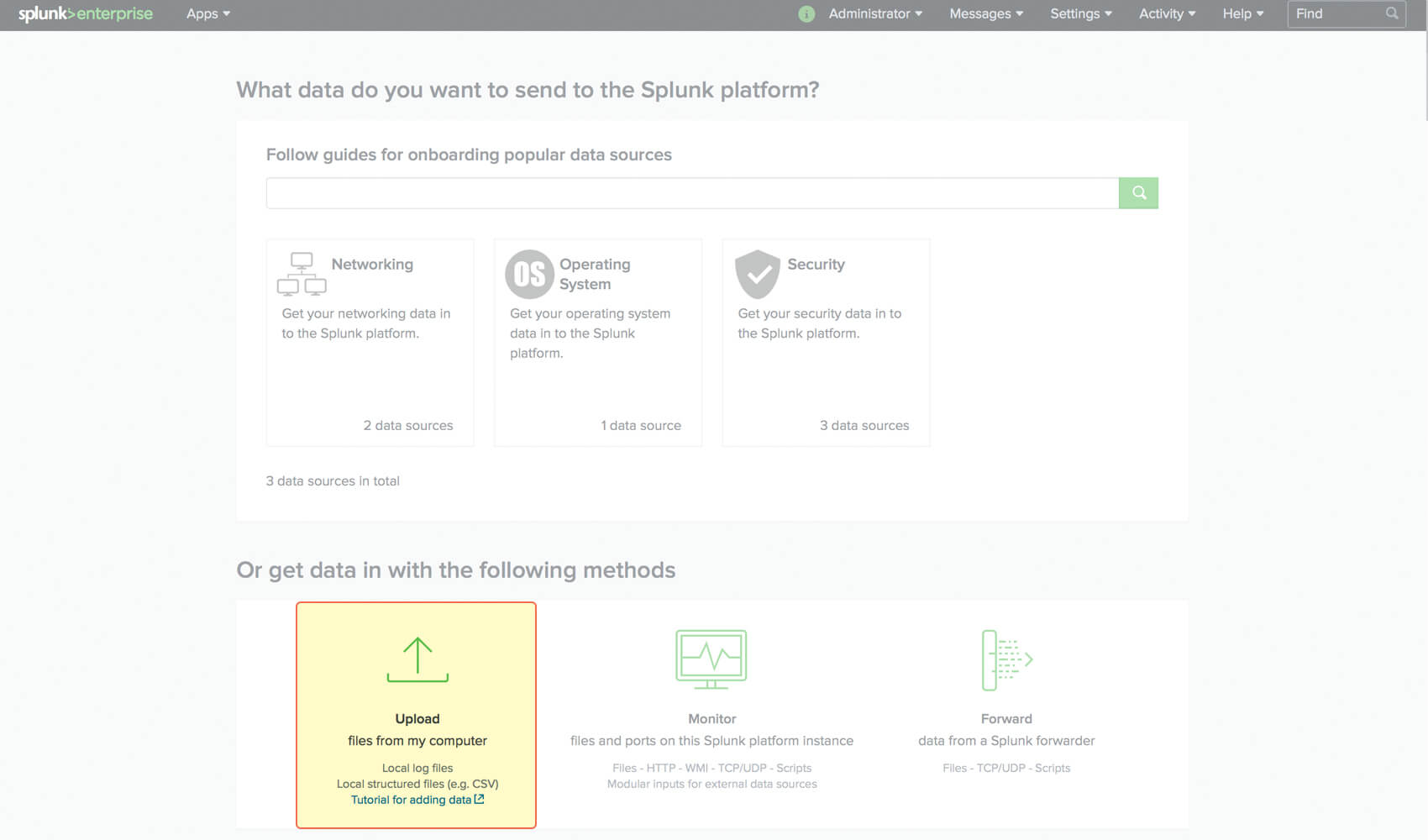
1. Add data to Splunk. In this tutorial, we use a CSV file which contains domain names, but feel free to use any other approaches described in the official Splunk documentation. Go to Settings > Add data.
2. Click Upload files from my computer.
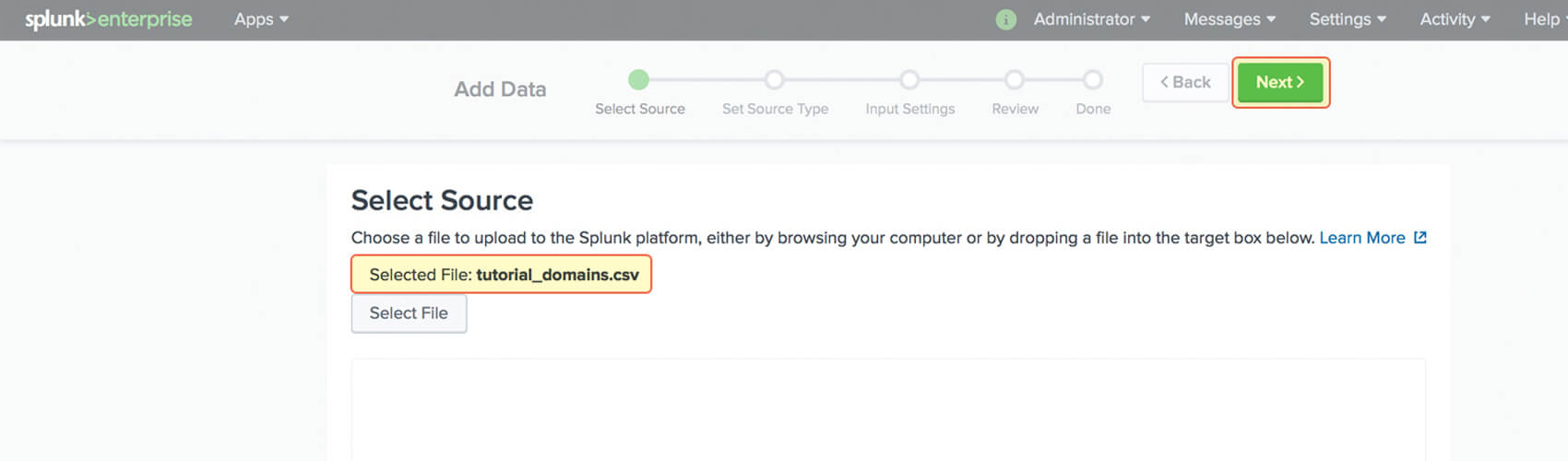
3. Select your file and click Next.
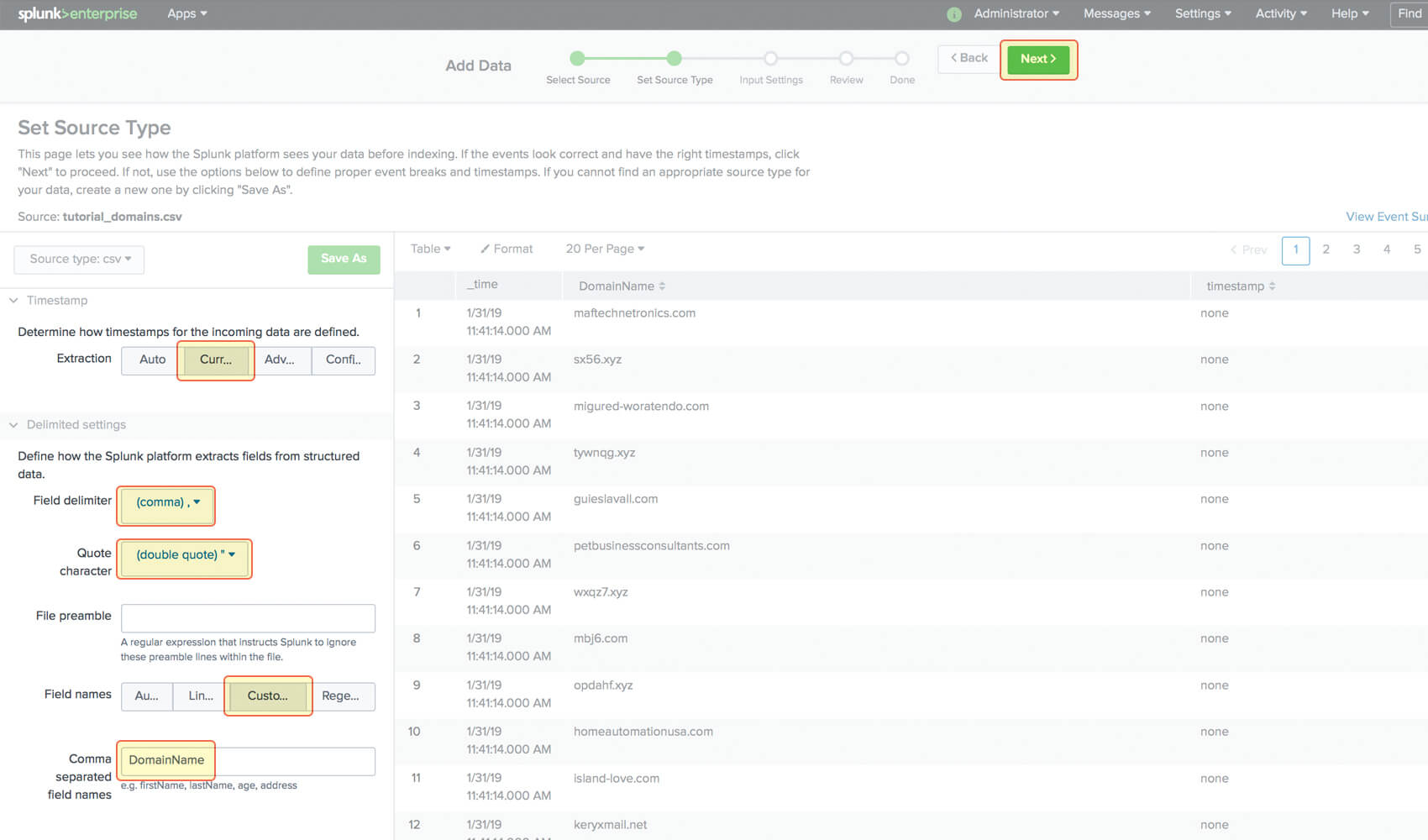
4. You need to configure the timestamp extraction (the name of the corresponding Splunk option on the view) as Current and fill in CSV columns names. Then click Next and choose whether you’d like to save the source type changes.
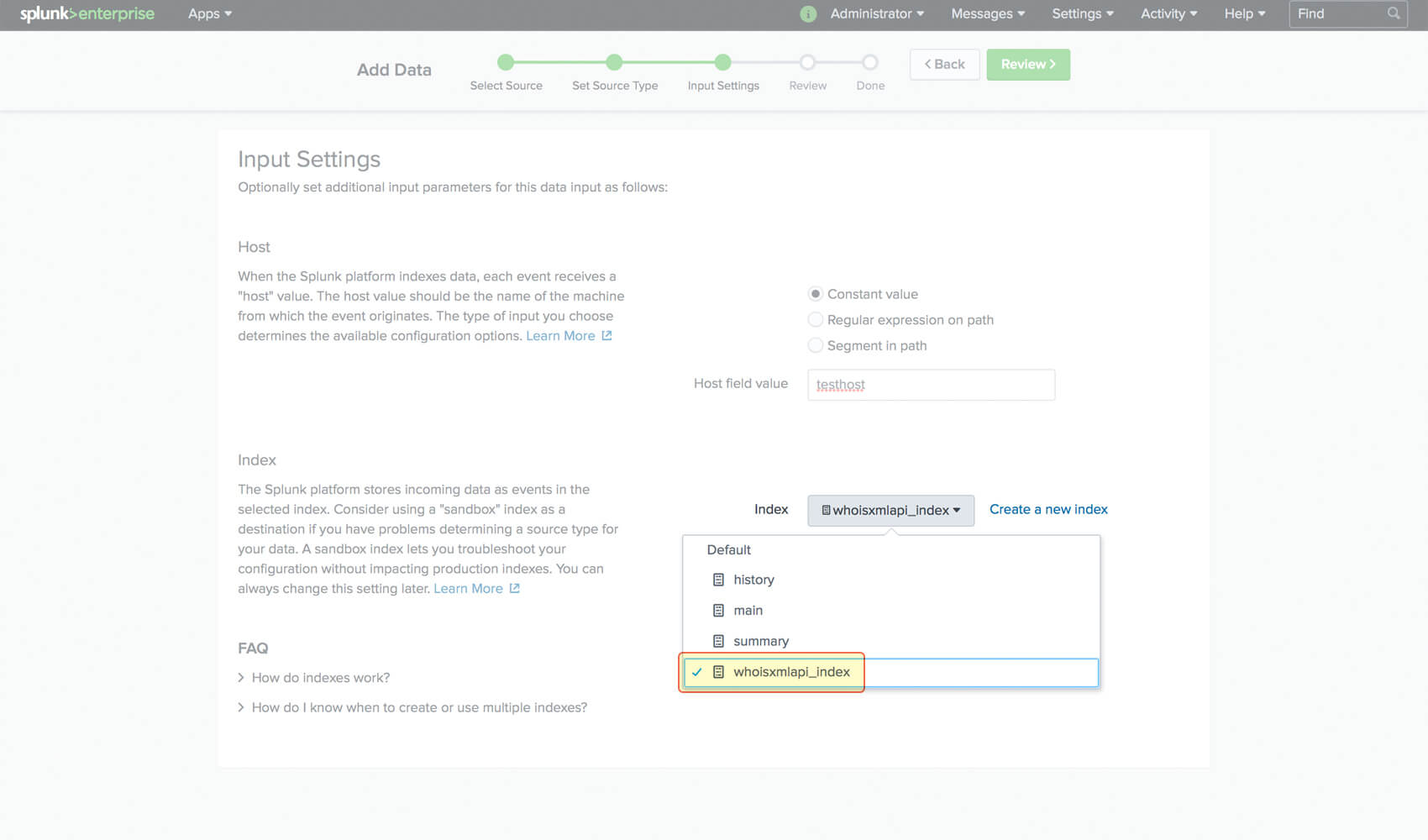
5. On the Input Settings page, choose the index to which you’d like to save your data. Then click Review.
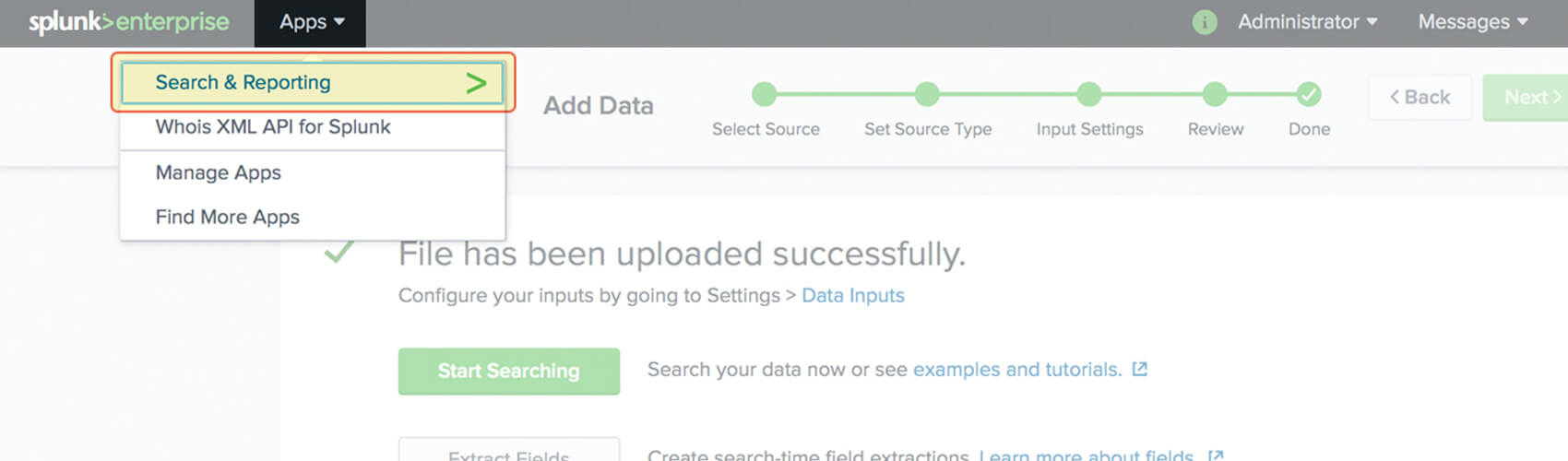
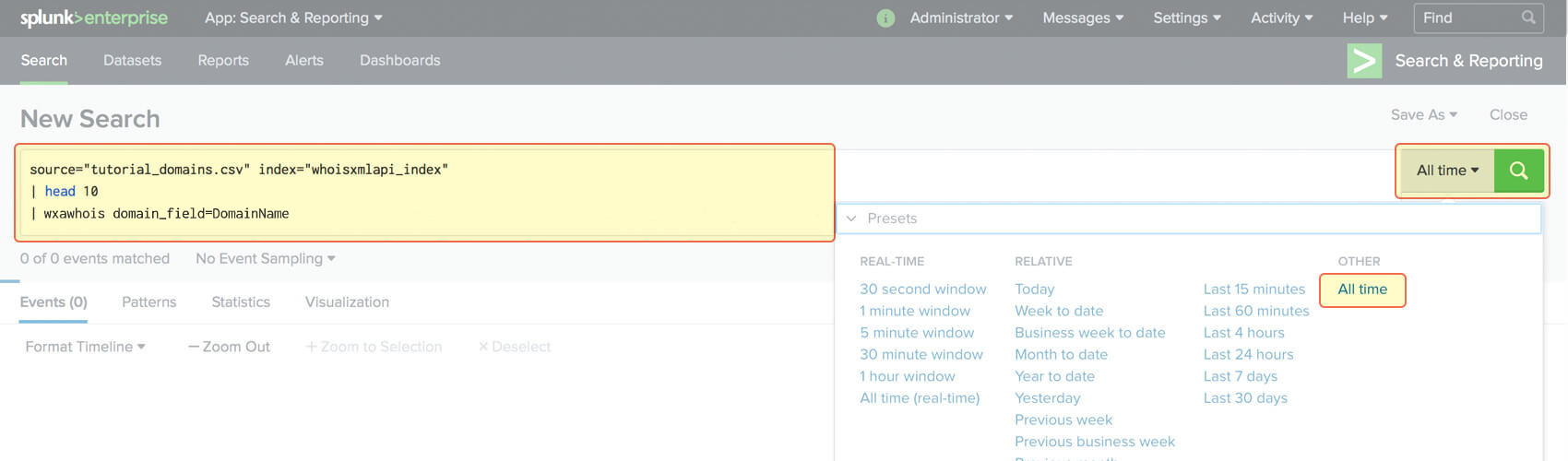
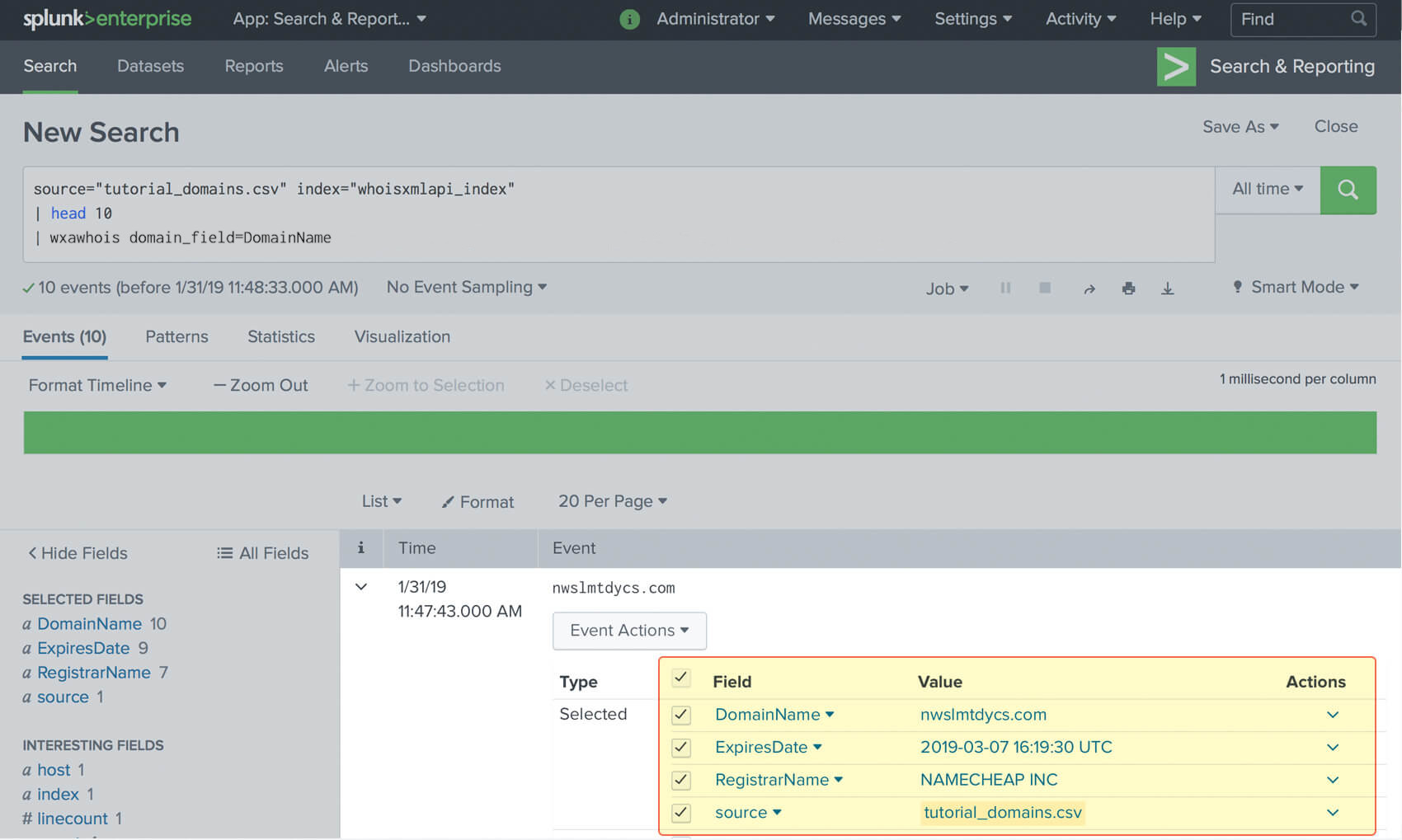
6. After reviewing, click Start searching or just go to Apps > Search & Reporting. You can add a lookup clause following your search query. Then choose the time period and click the Search icon.
7. Once the results have appeared, you can expand each event to see enriched properties. To perform a more comprehensive search, take a look at the corresponding official documentation.
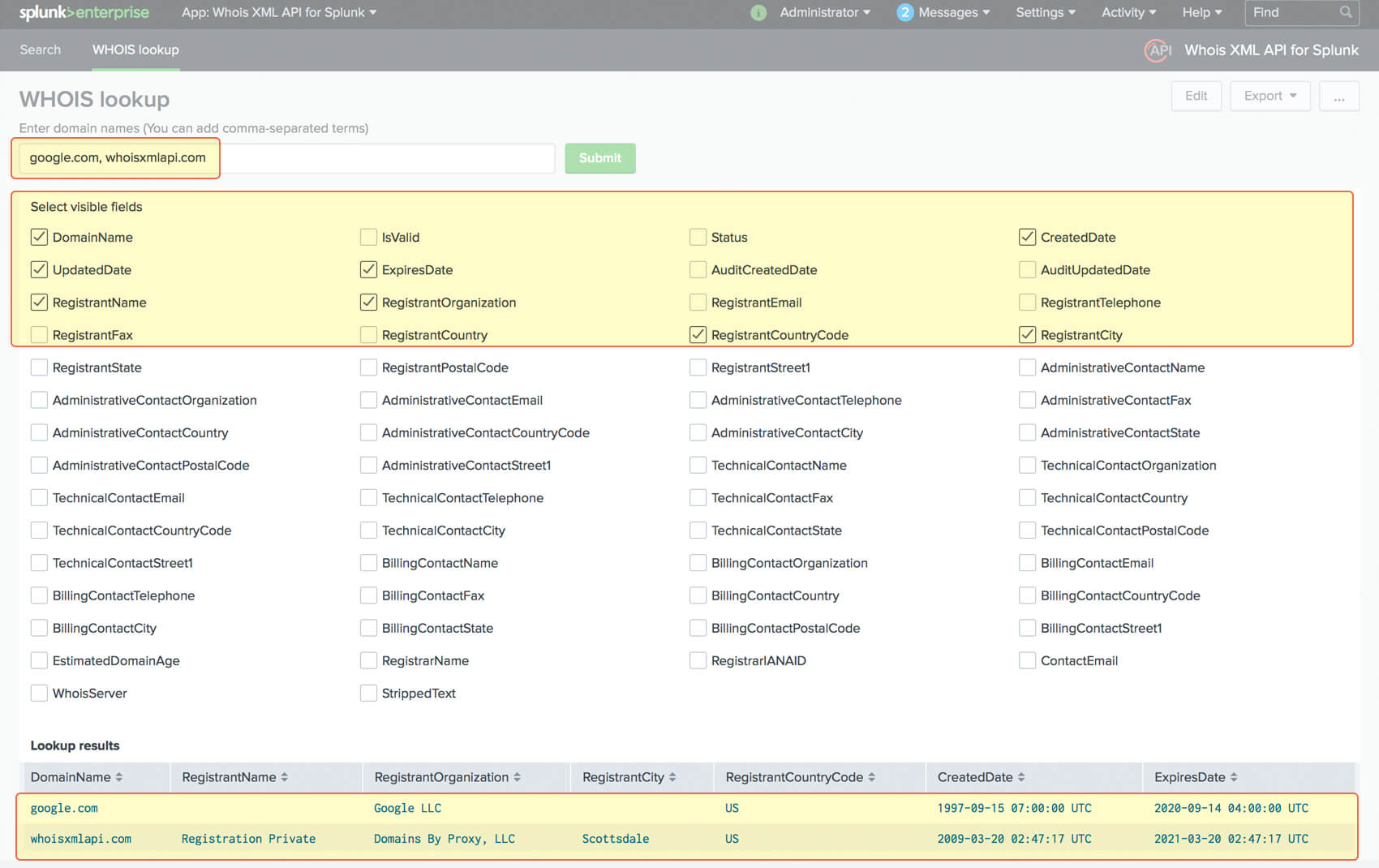
8. You can also perform instant WHOIS lookups from within the WHOIS Lookup page
Go to Apps > WhoisXML API for Splunk > WHOIS Lookup. Fill in one or more comma-separated domain names or IPv4 addresses. Select visible fields and submit the form.




































 WHOIS API Splunk application tutorial
WHOIS API Splunk application tutorial